Given the demands of hyper-growth, super efficiency and rapid digitalisation, the cloud has become the default for most, if not all, organisations. However, with the increase in cloud adoption, there is also an increase in data security risks. A survey by Security Magazine reveals that around 75% of the organisations have faced cybersecurity attacks in some form or the other. These include ransomware/malware, data breaches, and many more underlining the severity of the risk.
Therefore, to secure your company from untoward incidents like data breaches that put your company’s credibility at stake, you need a fool proof strategy. A tightly integrated GRC approach is a proven winner. In a cloud first world, enabling it with efficient cloud-specific tools like Cloud Posture Management (CSPM) solutions is key.
Let us try to understand the importance of GRC in cloud security and how CSPM tools can ensure a secure cloud environment.
What Is GRC?
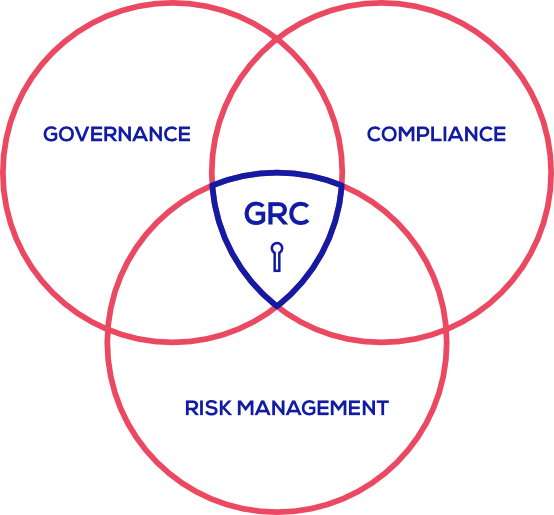
GRC is an acronym for governance, risk management and compliance. In the software world, it is a structured approach that organisations use to align IT practices with their core business objectives to free the organisation from cyber threats.
Governance refers to a process where management uses hierarchy or company policies to govern based on factual data and statistics. Risk management involves the evaluation of data and prioritising the same based on an overall risk assessment.
Compliance is the process of adhering to the rules of the market, organisation, and regulators or government in company operations.
GRC essentially guides enterprises to run their business within the constraints of law, finance, and compliance. Privacy policy, data share policy, compliance, risk estimation, finance, etc., all come under GRC.
With the dawn of the digital era, and businesses facing a paradigm shift towards cloud infrastructure, companies started facing cloud security issues, and multiple security disasters started to surface. It was in 2002 when Forrester put forward the need to use GRC as a marketplace tool.
GRC for Cloud Infrastructure Security

One of the hurdles that enterprises face while shifting to the cloud from on-premises is managing cloud risks while adhering to compliance. A well-planned and well-structured GRC provides a broader and more efficient approach for managing the cloud security risks of any organisation.
Even when companies adopt public cloud infrastructure, due importance to GRC should be a priority. When organisations broaden their GRC to the cloud, they get greater visibility to possible cloud risks. Risks that compromise the credibility and authenticity of the organisation.
A well-structured GRC strategy for cloud risks encompasses:
- Identifying cloud security assets and compliance
- Identifying data-related assets and compliance
- Embedding security control on cloud
- Monitoring and automating the overall cloud security compliance
- Continuously improving the security control processes
A strategically sound GRC helps the facilitators of cloud security practices like the CISOs of the company in many ways.
It empowers them with detailed and high-quality information that enhances decision-making capabilities. It also adds more agility, accountability and promotes a safe and productive working environment. In effect, it improves the overall performance of the organisation over a secure cloud.
To successfully implement GRC, organisations need to focus on chalking out an effective and holistic action plan leveraging the best CSPM tools.
Achieving GRC using CSPM Tools
CSPM or Cloud Security Posture Management tools are cloud security products that help companies achieve a secure cloud environment and adhere to the compliances. It is a cloud security solution that examines and compares an organisation’s cloud environment with a set of relevant compliance rules, best cloud security practices, and possible risks.
Gartner states that most of the cloud security breach is due to misconfiguration of the cloud environment. Misconfiguration can occur due to several reasons. The most common cause is a lack of visibility and understanding of cloud resources. This makes the cloud infrastructure vulnerable to data breaches and other security threats.
CSPM tools help organisations to mitigate such risks to up to 80%, as per this Gartner research. Some of the other ways CSPM tools benefit the organisations :
- Provide greater visibility across cloud platforms by monitoring cloud platforms in real-time
- Analyse the cloud data in real-time for any potential risks
- Continuously checking for any cloud compliance deviation
- Detect possible threats and remediates misconfiguration issues
Businesses are continuously evolving around cloud infrastructure. Therefore, cloud governance helps organisations centrally manage the resources without being vulnerable to malicious attackers. The role of CSPM in managing cloud-based services such as SaaS, PaaS, Iaas is therefore indispensable. Not only does it spot the security threats, but it also identifies areas of improvement. It empowers organisations with the rightful insights into implementing best compliance practices.
Cloudlytics CSPM tools enable businesses to bolster cloud posture and build a robust public cloud environment by achieving an optimum GRC. It is designed to enable organisations to follow the proper protocol and identify the potential security risks, provide appropriate and timely remedy all this while maintaining compliance with policies.
Conclusion
As digital transformation continues to drive companies towards cloud services, the need to escalate GRC from on-premises to cloud is inevitable. Deploying CSPM solutions is the first step towards ensuring a secure cloud environment as it helps organisations implement best GRC practices in the cloud.
Cloudlytics’ CSPM tools are an asset for organisations, especially those which leverage a complex cloud environment and multi-vendor support. It strengthens cloud security and helps organisations reap the true benefits of cloud computing.
Make your GRC water-tight with Cloudlytics CSPM. Book a free demo here
Further reading:
- Our e-book on CSPM called ‘A to Z of CSPM’
- 7 Best Practices for Cloud Security Monitoring



