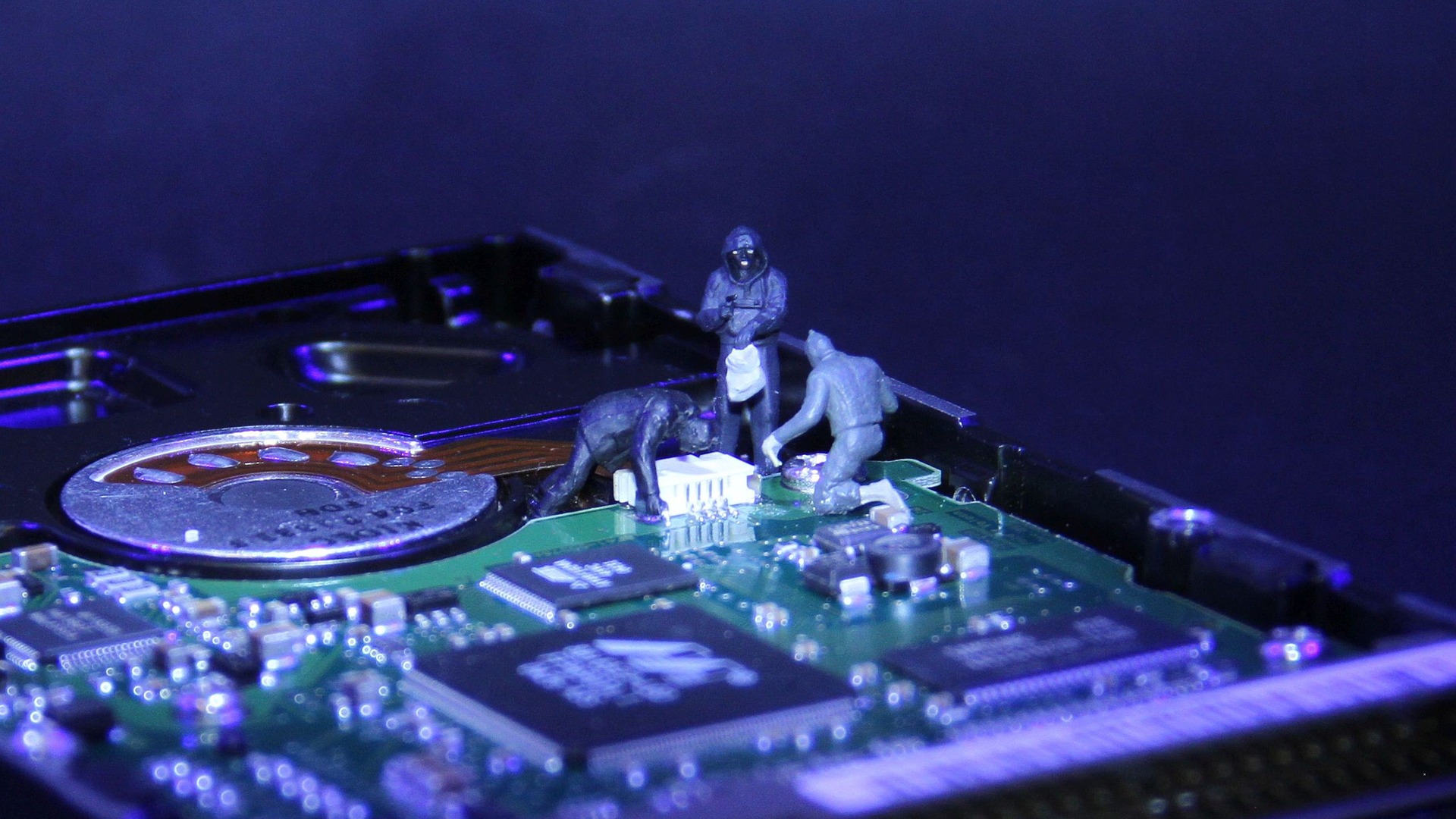
Data is a major asset for businesses in today’s digital world. Organizations are adopting modern technologies for data collection and processing. Big data systems are being leveraged to transform industries, improve business operations and predict trends. However, lack of a robust data security can open vulnerabilities that hackers can disrupt.
Big data security encompasses every security measure and tool used in analytics and data processes. Cyberattacks on big data systems, including ransomware, DDoS and other malicious activities, emerge from online as well as offline spheres. For organizations that store confidential data, the repercussions of information theft are huge. It is necessary for organizations to have a thorough understanding of ways to protect their big data systems against cybercriminals.
Major Areas to be Focused On
Hackers continue to find ways to infiltrate big data systems and steal valuable data. Business leaders must remain proactive, rather than being reactive, in case of data security breaches. These are some key areas that organizations must focus on to reduce their big data security risks.
Distributed Data
The data processing tasks are distributed by big data frameworks across several systems for rapid analysis. These distributed systems avoid creating a single point of failure and balance the load. However, these systems are highly vulnerable to security threats and hackers can infiltrate the entire network by attacking just one system. Security measures such as intrusion prevention systems enable the security team of an organization to safeguard their big data platforms against such threats via network traffic examination. In addition, encryption tools can be used to operate on various big data storage formats.
Endpoint Vulnerabilities
The data on endpoint devices can be manipulated by cybercriminals and false data can be transmitted to data lakes. It is necessary that organizations adopt security solutions that perform analysis on logs from endpoints and validate the legitimacy of the endpoints. Fraud detection technologies enable organizations to prevent such vulnerabilities. These keep hackers from accessing systems and disrupt malfunctions in processes.
Cloud Security
Data created by big data systems are usually stored on the cloud, which are potentially at risk. Inaccurate encryption of the data and improper security measures make it easier for hackers to access sensitive data, In order to fix these issues, organizations must encrypt every sensitive data and implement IPS for detection of network intruders. In addition, organizations can implement multi-factor authentication along with biometric data and passwords. These authentication mechanisms will help organizations protect the sensitive data against cyberattacks.
To Sum Up
Most organizations are leveraging big data analytics tools for improving business strategies and this has opened possibilities for cybercriminals to infiltrate the big data architecture. The list of big data security issues continues to grow, which have given rise to several government regulations and privacy concerns regarding big data systems.
In the world of modern businesses, data is the fuel while the challenge lies in consistent access to the right data at the right time. Meanwhile, organizations must see that their data remains kept from falling into wrong hands. Organizations across the globe are continuously searching for a balance between data agility and self service analytics. All this while taking consistent actions to reduce risks to their big data systems.
What do you need to make your cloud 100% secure? Consult the cloud experts who have done it for many clients. Book an appointment here