In 2019, at the Bloomberg “Women in Fintech platform” event, there was some great discussion on the growth trajectory of the fintech industry.
Initially, the expert panel agreed that public clouds and fintech startups are a match made in heaven. One of the experts, a member of Amazon’s Fintech startup development team, Kathryn Van Nuys, made an excellent point:
“The cloud has significantly lowered the barrier to entry for startups as they can launch and scale products, instantly paying for IT as they consume it, as opposed to needing to make a significant upfront investment in servers and infrastructure.“
Many industry leaders share the same point of view. 55% of them are already using multiple public clouds, the 2020 IDG cloud computing study revealed. Even a good number of companies have dedicated ~30% of their IT budget to this purpose. Expecting exponential growth in public cloud adoption is only logical.
However, despite its advantages, a public cloud isn’t all sunshine and rainbows.
First, there is a knowledge gap. Many companies struggle to understand how to secure data, stick to Fintech compliance guidelines, and hold it accountable for a breach. New policies and online threats add more to this confusion.
Second, public clouds are not impregnable. There are enough horror stories of massive data breaches that led to the demise of otherwise successful companies.
As a Fintech leader, if you are worried about public cloud security or just hesitant to “go cloud,” this article will answer your questions.
Public cloud and Fintech: Not such a ‘match made in heaven’
Despite all the good reputation, public clouds enjoy from the Fintech community, underlying concerns exist.
In a Cybersecurity survey, 52 % of respondents expressed that the chances of security breaches are higher in public clouds. And their concern is valid. Even some of the biggest brands could not protect themselves from hackers.
>500k
Zoom accounts were breached and their data was sold on the dark web, in April 2020. As per sources, hackers used previously leaked accounts to invade and compromise Zoom databases.
100 million
accounts of Mobikwik, a leading Indian Fintech platform, were attacked in March 2021. User data was available for sale on the dark web.
7.5 million
banking users of Dave, the US Fintech giant, were attacked in July 2020. User data was available for sale on the dark web.
These are some well-known examples. There were many more disasters we know nothing about that killed companies and put users at risk.
Spotting the Achilles’ heel: Vulnerabilities of cloud security
Public cloud infrastructure always comes with built-in cloud security. However, human error, lack of visibility, and the very nature of the cloud tech model expose some significant weak spots, such as:
Misconfiguration
Public infrastructures are designed for easy data sharing and scalability. This accessible data sharing feature opens up some potential risks. Usually, you can solve this with a suitable configuration. However, 55% of companies aren’t very familiar with cloud security configurations. Hackers can use these security loopholes to stage their attacks.

Unauthorized access
When your data is on the cloud, you lose visibility to some extent. Of course, cloud service providers do their best to ensure security, but there is a chance someone from their team used a weak login password or didn’t pay attention. If attackers find the access, they can easily bypass security walls and steal your data.
APIs
CSPs often offer APIs to their customers. The latest studies show two-thirds of enterprises give access to these APIs to external developers and business partners. If there are some vulnerabilities, potential hackers use those to wreak havoc. According to Gartner, APIs will be targeted more frequently by 2022.
Contractual loopholes and breaches
For fintech companies moving to the cloud, contracts are crucial. Many large public cloud infrastructure providers add a clause that they own the right to sell your data (your user data) to third parties. If your user data got compromised, “legally” or not, it’s terrible news. Also, some unscrupulous Cloud Service Providers (CSP) may themselves breach the contract and misuse your data.
Ensuring cloud security
To make your fintech security ironclad, here are some suggestions, albeit not exhaustive. But this can surely be your first step to increased cloud security.
Embrace a shared security model
Reputed public cloud providers like AWS and Microsoft Azure follow a shared security model. In simpler terms, you will be responsible for your data security and applications running in the cloud. It’s the CSP’s responsibility to ensure their platform is secure, updated, and always on. This model gives you great control over data encryption, fintech compliances, and data access.
Secure your APIs
Get your developers to design APIs with multiple authentications, encryption, and access control.
You can even conduct penetration tests to identify any loopholes and get a secure code review. Also, use SSL/TLS encryption for improved security. Multi-layer authentication with schemes like OTP, digital identities are also helpful.
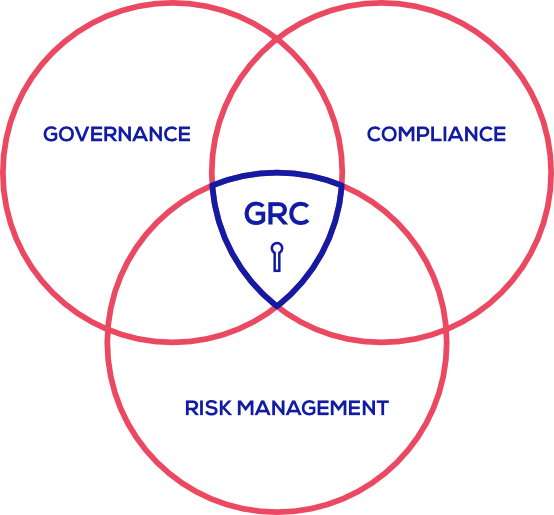
Consider using CSPM (Cloud Security Posture Management)
Misconfiguration of your public cloud environment is one of the biggest security threats out there. For any fintech company, any breach can be fatal as their user data is super confidential to begin with.
CSPM tools can be lifesavers here. These are designed to identify and resolve configuration issues and fintech compliance risks.
Widely used CSPM tools are capable of :
- Spotting and resolving misconfiguration issues
- Remembering and utilizing different sets of best practices for different cloud configurations and services
- Monitoring storage, encryption & account permissions, and compliance risks
For example, Cloudlytics ticks all the boxes mentioned above and then brings some more to the table. It’s on constant watch and spots any potential weakness long before the disaster can take place. You get all reports and data presented to you in an easily understandable and visually attractive manner at any time. It’s like having a guard to watch over your public cloud security.